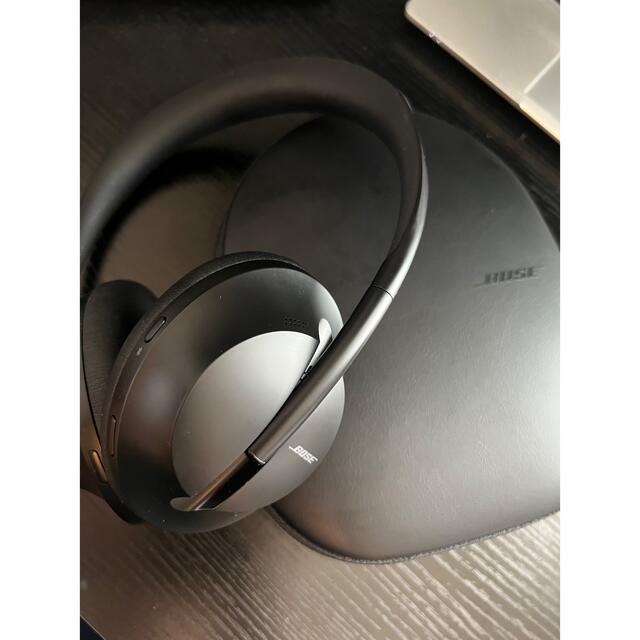
美品 BOSE ノイズキャンセリング ワイヤレス ヘッドホン NC700
(税込) 送料込み
商品の説明
BOSE ノイズキャンセリング ワイヤレス ヘッドホン NC700 ブラック
一年ほど前に購入しましたが、数回だけ使用し使わなくなったので、出品致します。
ほど、新品の状態で購入致しました。箱もコードもすべて揃っています。本体も美品となっております。
ですが、中古品ということをご理解の上ご購入ください。
ご質問等ございましたら、コメントお願い致します。
よろしくお願い申し上げます。
#bose #ボーズ #nc700 #ヘッドフォン #ワイヤレスヘッドフォン #ノイズキャンセリング商品の情報
| カテゴリー | 家電・スマホ・カメラ > オーディオ機器 > ヘッドフォン |
|---|---|
| ブランド | ボーズ |
| 商品の状態 | 未使用に近い |

美品】Bose NC700 ノイズキャンセリング Headphones - ヘッドフォン

Amazon.co.jp: Bose Noise Cancelling Headphones 700 ワイヤレス

BOSE ノイズキャンセリング ワイヤレス ヘッドホン NC700 ブラック-

内祝い】 ノイズキャンセリングヘッドホン BOSE Quiet 開封新古品 II
高品質の激安 QuietComfort Bose ヘッドホン □新品未開封 BOSE ボーズ

【極美品】BOSE ノイズキャンセリング かえるの様専用BOSE ワイヤレス ヘッドホン ヘッドフォン 純正売品 NC700 NC700

いいスタイル BOSE ワイヤレス ヘッドホン NOISE ノイズキャンセリング

BOSE ノイズキャンセリング ワイヤレス ヘッドホン NC700 ブラック-

BOSE ノイズキャンセリング ワイヤレス ヘッドホン NC700 ブラック

Amazon.co.jp: Bose Noise Cancelling Headphones 700 ワイヤレス

在庫一掃】 【美品】Bose NC700 ヘッドホン700 Cancelling Noise BOSE

BOSE ノイズキャンセリング ワイヤレス ヘッドホン NC700 ブラック
Bose Noise Cancelling Headphones 700 ワイヤレスヘッドホン USED美品

BOSE ノイズキャンセリング ワイヤレス ヘッドホン NC700 ブラック

BOSE ノイズキャンセリング ワイヤレス ヘッドホン NC700 ブラック-

本物保証新品 ヘッドホン ボーズ BOSE NCHDPHS700SLV Bose Noise

オリジナルのbosenc700ヘッドセット,Bluetoothワイヤレス,スポーツ

Amazon.co.jp: Bose NC700 Noise Cancelling Headphones 700 - Black

美品 BOSE ノイズキャンセリング ワイヤレス ヘッドホン NC700 - 通販
Bose Noise Cancelling Headphones 700 ワイヤレスヘッドホン USED美品

送料0円 BOSE NC700 ヘッドホン ノイズキャンセリング kochmetal.com.br

BOSE - BOSE ノイズキャンセリング ワイヤレス ヘッドホン NC700

正規店国産 BOSE ワイヤレスヘッドホン ノイズキャンセリング対応
![美品] BOSE 700 ノイズキャンセリング ワイヤレス ヘッドホン www](https://static.mercdn.net/item/detail/orig/photos/m29297511015_1.jpg)
美品] BOSE 700 ノイズキャンセリング ワイヤレス ヘッドホン www

人気最新作】 BOSE ノイズキャンセリング ワイヤレス ヘッドホン NC700

Amazon.co.jp: BOSE NOISE CANCELLING HEADPHONES 700 ワイヤレス

最終値引】BOSE NC700 ボーズ ノイズキャンセリングヘッドホン

殿堂 即決! BOSE 3 中古品 Comfort ノイズキャンセリング ヘッドホン
Bose Noise Cancelling Headphones 700 ワイヤレスヘッドホン USED美品

春新作の 美品❗️【BOSE】NOISE 700 CANCELLING ヘッドフォン

BOSE ノイズキャンセリングヘッドホン700 | ビックカメラ.com

BOSE ノイズキャンセリング ワイヤレス ヘッドホン NC700 ブラック
BOSE NC 700 ノイズキャンセリングヘッドセット ほぼ未使用

国内正規品】 BOSE ワイヤレス ノイズキャンセリング ワイヤレス BOSE

ボーズ(BOSE)|ノイズキャンセリングヘッドホン|HARDOFFオフモール

最終値引】BOSE NC700 ボーズ ノイズキャンセリングヘッドホン
Bose Noise Cancelling Headphones 700 ワイヤレスヘッドホン USED美品

お見舞い 【美品】Bose NC700 ヘッドホン700 Cancelling Noise BOSE

Amazon.co.jp: Bose NC700 Noise Cancelling Headphones 700 - Black

オリジナルのbosenc700ヘッドセット,Bluetoothワイヤレス,スポーツ







商品の情報
メルカリ安心への取り組み
お金は事務局に支払われ、評価後に振り込まれます
出品者
スピード発送
この出品者は平均24時間以内に発送しています














